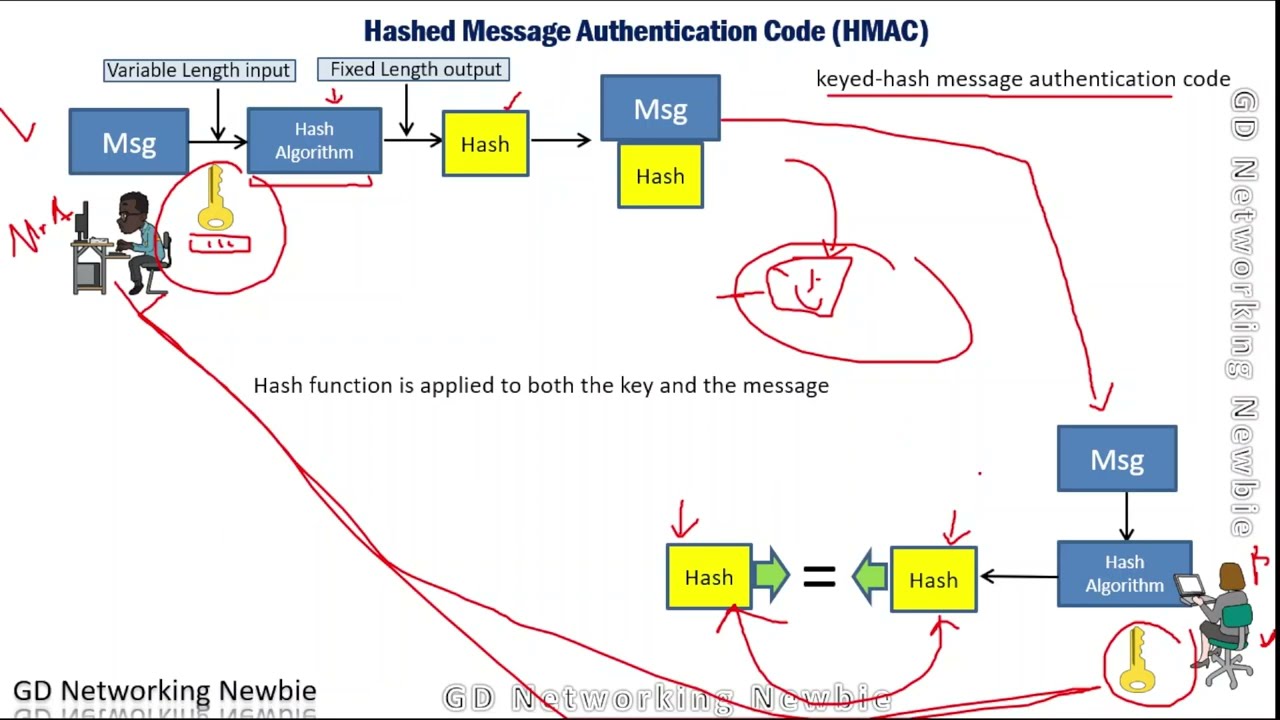
Text data size. Up: before AES-HMAC encryption and down: after AES-HMAC... | Download Scientific Diagram
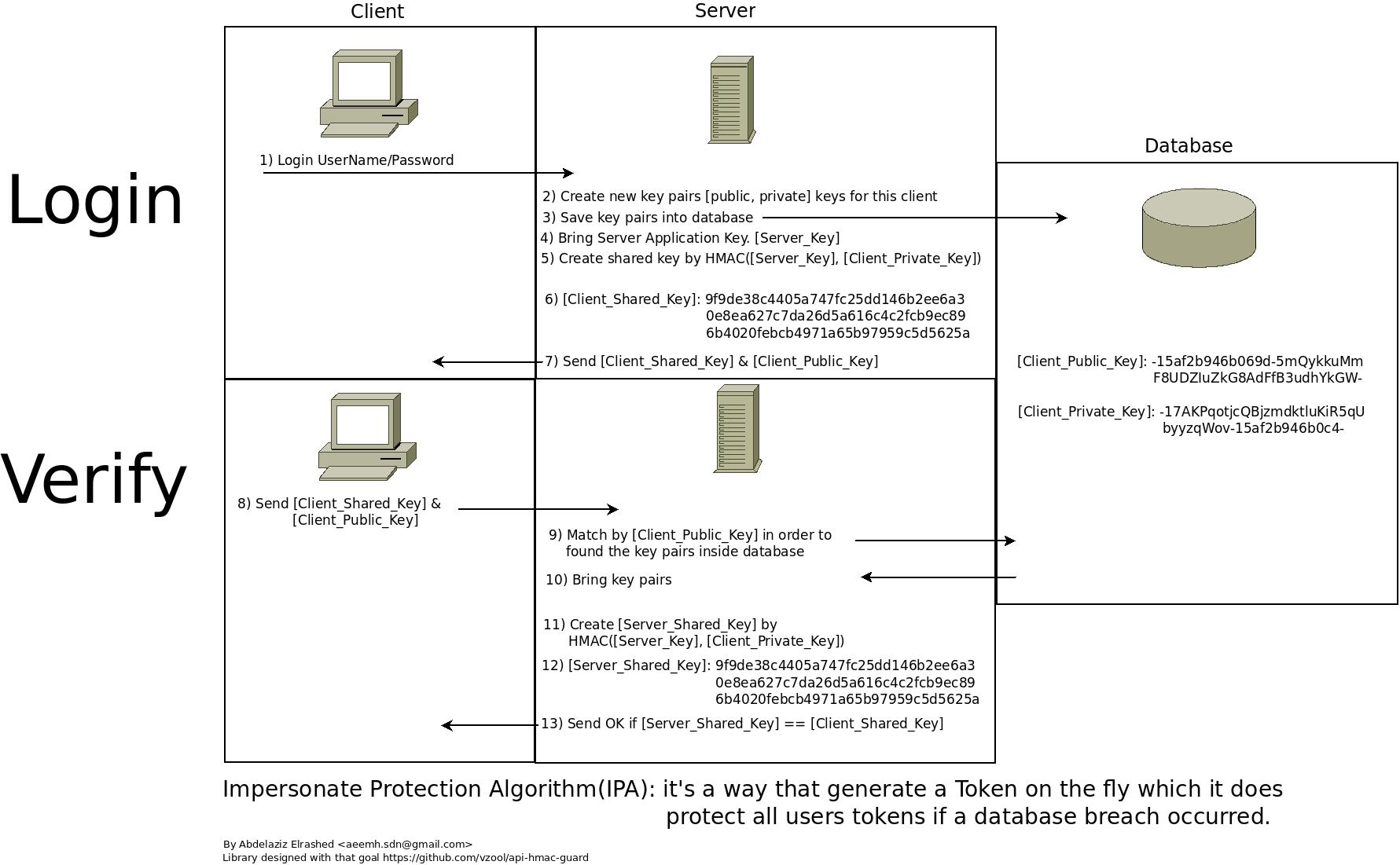
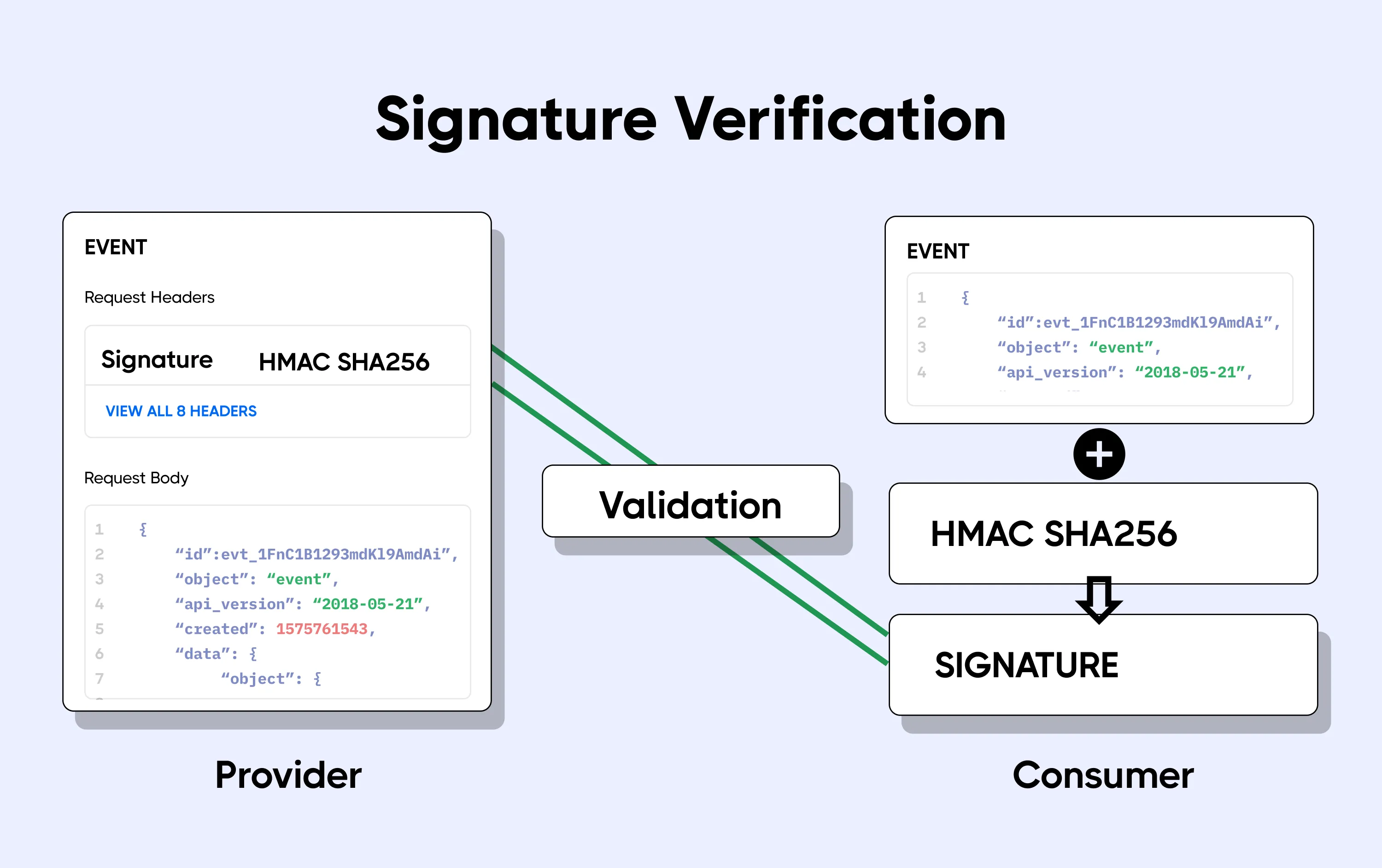
GitHub - vzool/api-hmac-guard: A simple and secure way of authenticating your RESTful APIs with HMAC keys using Laravel

Processing time to compute HMAC-SHA-256 and HMAC-SHA-384 with keys of... | Download Scientific Diagram